- What are the risks associated with investment?
- How hostile investment could damage your company
- How hostile investment could affect the UK's national security
- How can you take control of your investment security?
- Assessing the risks
- Protecting your company
- Ensuring your mitigations work
- What does the NSI Act mean for your business?
- Your obligations
- The Governments' obligations
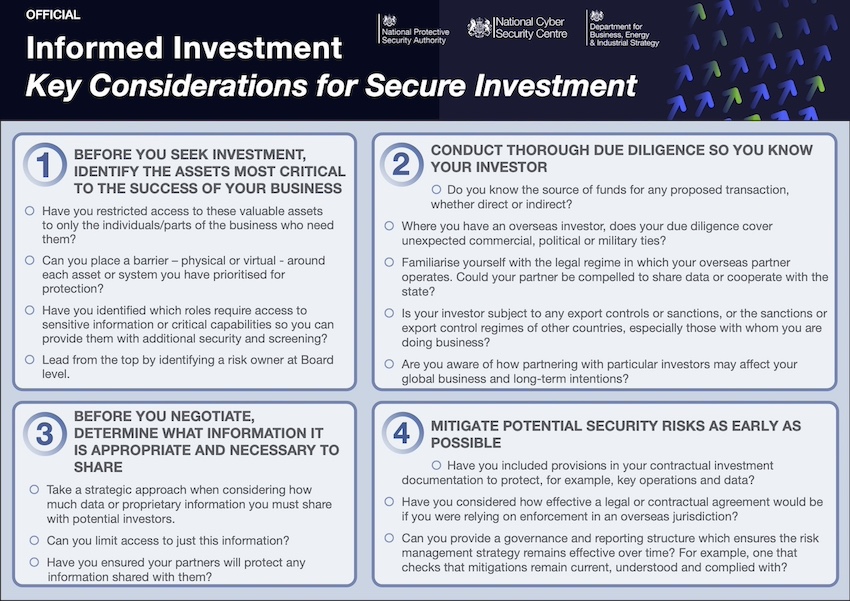
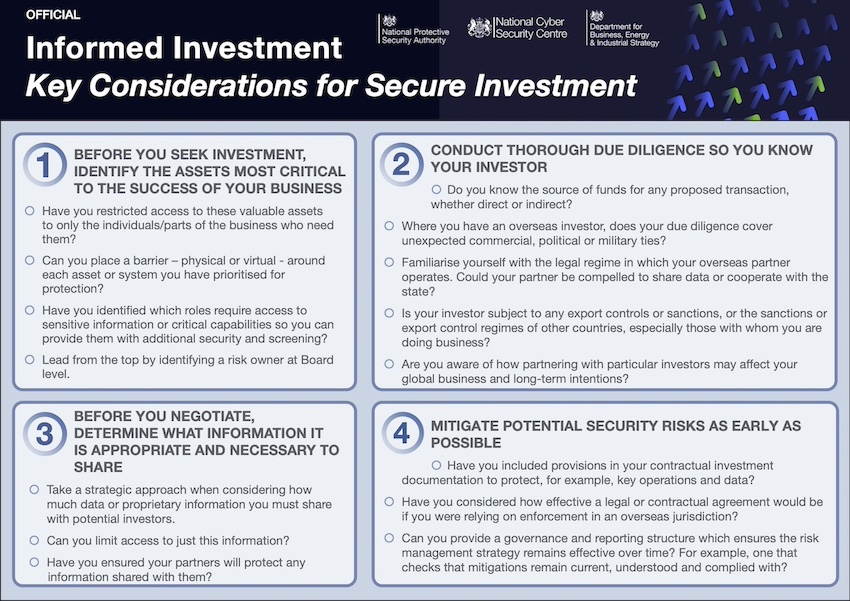
- Informed Investment at a glance
The UK thrives on and welcomes domestic and foreign investment. 2020 saw UK startups and scaleups attract record investment with $15 billion (£11.2 billion) in venture-capital funding.1 In the same year, the UK saw record levels of equity investment in smaller UK businesses - 8.8 billion.2 Such finance is vital in enabling UK businesses, and the UK economy more broadly, to grow and prosper.
However, in a small number of cases, investments could potentially present a risk to UK national security.
This guidance is for businesses of any size seeking investment. It covers potential risks associated with investment - both to your business and the UK's national security - and how taking a security-minded approach from the start of your investment planning can reduce these risks. It also outlines what the new National Security and Investment Act 2021 may mean for your business.
You can also find a summary of this guidance in our Key Considerations for Secure Investment.
The National Security and Investment Act 2021 (NSI Act)
The NSI Act gives businesses and investors the certainty and transparency they need to do business in the UK while protecting the UK's national security. It provides the Government with powers to scrutinise and intervene in acquisitions of control of qualifying entities and assets. The legislation came into force on 4 January 2022 and the call-in power in the Act may be used in relation to acquisitions that have taken place since 12 November 2020.
Further information on the NSI Act is available at GOV.UK.
Adhering to the following guidance does not guarantee that an acquisition will not be called in or be blocked or face other remedies under the Act. Whilst there are no guarantees, it may reduce any potential risks to national security and therefore the likelihood of the Government taking such actions.
What are the risks associated with investment?
In a minority of cases, the investment that you are seeking may unintentionally pose a risk to your company's, and the UK's, security. For example, the acquisition of a sensitive part of your business by another UK company with poor information security may result in risks to data security as well as national security.
Case study: investment that would result in the degradation of UK capability
A UK robotics company was involved in the world-leading research, development, design and production of small but novel components. This company sought investment from a UK acquirer, which openly said that it wanted to save costs and close the part of the business where sensitive R&D of benefit to UK national security took place. Soon after the acquisition was completed, this part of the business was closed. The unintended consequence was the degradation of a unique UK capability.
Less frequently, the parties that you do business with may use domestic or foreign investment to gain access and influence, either to harm your company's interests or the UK's national security. This could include using information from your company to undermine your competitiveness. We call these parties hostile actors.
How hostile investment could damage your company
Hostile investors can potentially gain access to non-public information about your business, such as:
- ideas, information or techniques that have industrial, commercial or other economic value
- research data
- financial and personal information
- information on your customers or suppliers
- commercially sensitive material
In the hands of a hostile actor, this access could be used to harm the interests of your company, for instance to influence decision-making, undermine competitive advantage, and advance the hostile actor's interests. It does not matter if the information is gained through legitimate or illegitimate means if the intention for its use is hostile.
As well as serious financial damage, hostile actors can cause reputational harm to UK businesses. For example, they could do this by using the UK company's technological and military capabilities in a manner incompatible with the business's original intentions or values, such as to expand social control and limit individual freedoms.
In some cases, your investors may impact your ability to win future contracts. For example, the Ministry of Defence (MOD) is one of the biggest public procurement organisations in Europe and manages some of the most complex and technologically advanced requirements in the world. Being a part of the UK Government's supply chain presents opportunities for an organisation to be at the leading edge of innovation. However, the sensitivities of the UK Government and MOD's work mean that they expect suppliers to consider the risks involved with seeking investment and mitigate them effectively. The same is likely to be true if you are seeking contracts with overseas governments.
How hostile investment could affect the UK's national security
Hostile actors can, at times, be backed by a foreign state, whose aims may be at odds with UK interests. These actors may exploit investment, potentially over the long term, for example to:
- develop a research and innovation foothold to increase military and technological advantage over the UK and other countries
- position themselves in an area of the UK's critical infrastructure which they could use to their advantage
The UK's thriving research and innovation base may make it attractive to hostile actors seeking to gain influence over a UK organisation or more broadly, such as over a technology or sector.
How can you take control of your investment security?
This section shows the steps you can take to identify and mitigate potential security risks as you seek investment. Taking a security-minded approach from the start will enable you to make well-informed decisions and potentially manage your risk sufficiently to avoid your transaction raising national security concerns and being considered under the NSI Act. Good security can also protect your competitive advantage and make your company more attractive to investors and customers.
This means:
- assessing the potential risks associated with a prospective investor, based on an understanding of their risk profile and where your organisation's value lies
- considering early (ideally before seeking investment) appropriate legal, physical, cyber and personnel security measures to protect the value in your business
- if you do decide to proceed with the investment, ensuring those security measures will endure for the duration of your relationship with the investor
Assessing the risks
Conducting an early risk assessment will help you to be better informed about possible outcomes, plan mitigations, and have a stronger negotiating position.
Understand what matters to your business
Knowing what is most valuable to you will help you to determine what you may need to protect.
- Do you understand which assets are most critical to the existence and success of your business? These could include knowledge, information, data, processes, products, services, staff, customers or premises. NPSA's Asset Identification Guide can help you decide what is critical; advice is also available for technology startups in our Secure Innovation guidance.
- If your potential investor is an overseas party, have you determined what data and information is appropriate to share and where it will be held? Personal data should only be transferred outside the UK if there is a legal basis for the transfer that satisfies one of the grounds in the UK GDPR, for example the transfer is to a third country that ensures an adequate level of protection.
On any potential investment, looking beyond your business can help you to identify wider issues that could raise national security concerns. Supply chains are often targeted by hostile actors as an easier way to get access to the information and assets they want. This can include your suppliers and the supply chains you are part of. If you are a supplier to a sensitive or critical entity, then their national security concerns will be just as relevant to you. Have you discussed any potential investors with the companies you supply, accounting for any non-disclosure agreement (NDA) obligations you might have? Does your contract with them preclude any such investment?
Research your investor
We recommend conducting a thorough due diligence investigation into parties you are seeking investment from, to include:
- any related parties, including all members of an investment consortium, any fund manager and any other alternative contacts
- the source of the funds
- any unexpected commercial, political or military ties
- consideration of whether the parties are subject to UK export controls or sanctions or the sanctions or export control regimes of other countries, for example the US ITAR, especially those with whom you are doing business
Hostile investors may seek to obfuscate their identity, for example by funnelling investment through a UK-based company and/or corporate structure. It pays to understand who you are really dealing with behind the scenes.
Consider the impact of the legal regime under which your proposed investor operates. Overseas parties might operate under regimes that could compel them to release data or cooperate with their state.
For example...
Russia has an extensive lawful intercept capability, known as the System of Operative Search Measures (SORM). SORM allows Russia's domestic intelligence agency, the Federal Security Service (FSB), to covertly monitor communications to, within, and out of Russia. The FSB can also compel companies and individuals to share data stored in Russian with them and could prevent the data holder from disclosing this to the data owner.
All communication service providers (CSPs) operating in Russia are obliged to install equipment to enable the FSB to monitor communications. The FSB is not obliged to provide CSPs or commercial companies with any details of their monitoring of SORM.
This may mean that you are unaware of how your sensitive communications and information may be used outside your commercial engagements in Russia or with Russian individuals and companies.
A foreign state may be able to exercise influence or control over your business even if the investor you are dealing with does not appear to be state-owned.
For example...
Chinas National Intelligence Law allows Chinese intelligence agencies to compel Chinese organisations and individuals to carry out work on their behalf and provide support, assistance and cooperation on request.
This law may affect the level of control you have over your information and assets as you engage with Chinese individuals and organisations, especially if you work in an area that is of interest to the Chinese state.
A UK government website provides guidance on managing ethical, legal and commercial matters when working in China or with Chinese companies.
Protecting your company
You can take steps to mitigate the risks associated with a proposed investment. We recommend considering mitigation measures early so that:
- you limit or protect any sensitive information shared with potential investors, both before and after any investment
- you consider commercial options and address risks upfront by modifying the terms of the deal
- mitigations can be agreed and implemented prior to any in-depth engagement
Case Study: limiting access to sensitive areas
A large genetics company was in talks with a foreign company to invest in the manufacturing of its goods.
The investing company's country of origin could be considered a hostile environment, with strong state intervention and a publicly-stated intention to develop its capabilities in the company's specialist area. With the company beholden to the state's laws, there was a chance it could be placed in a compromising situation.
To protect its long-term competitive advantage while minimising short term operating costs, the company ring-fenced all sensitive knowledge, research and development in its home state, while only procuring investment in parts of its manufacturing business.
Whether you can mitigate risks to an acceptable level will depend on the threats your organisation faces and your risk appetite. If a foreign consortium intends to buy a minority stake in your business and you have concerns about one of the members of the consortium, you may be able to rely on the remaining members to ensure any conditions are complied with. However, if you are giving up control of a large part of your organisation, any risks will become increasingly difficult to manage.
What should you consider when creating a Joint Venture (JV)?
Setting up a JV can have significant commercial benefits in combining your company's expertise with that of your JV partner. However, you should be aware of the risks.
By sharing trade secrets with your JV partner, your business could be at risk of losing exclusive access to that knowledge. You could soon find similar products competing against you in the market. Certain countries encourage or compel domestic companies to share non-public information with the state and possibly other domestic companies.
You should consider mitigations early in the process. Where feasible, mitigations could include setting up a JV which is solely focused on older models of your product or technical knowledge, so safeguarding your competitive advantage.
Your security solution is likely to be more effective if it considers physical, personnel, technical and cyber elements as complementary to each other. As you start to look at existing and proposed security measures, here are some things to consider. The size of your company and workforce may influence which measures you implement. You may also have other considerations depending on your context.
- Are you aware of how individual investments may affect your global business and your long-term intentions?
- Can you provide a governance and reporting structure which ensures the risk management strategy remains effective over time?
- NPSA/NCSC guidance Secure Innovation provides advice for technology startups on early steps to establish a strong security culture and leadership, including when working internationally.
- For larger companies, Secure Business supports leaders to operate securely with overseas parties.
- NPSAs Passport to Good Security.
- Consider including the following provisions in your contractual investment documentation:
- protecting the retention of the current supply chain, or ensuring that control over your supply chain rests with existing management
- maintaining control of operations and data in the UK
- requiring a notification if the investor undergoes any change of control, change of jurisdiction or if any of their key personnel change
- How will you ensure that your partners and suppliers protect the system access and information that you have shared with them?
- A good NDA restricts the use of your ideas and information to a specific permitted purpose. It should be as specific as possible. However, it is worth being realistic about how your partners need to use the information - for example, allowing confidential disclosures to employees and professional advisors where necessary. The Intellectual Property Office offers guidance on using NDAs to keep your invention a secret when talking to others.
- Have you considered how effective a legal or contractual arrangement would be if you were relying on enforcement in an overseas jurisdiction? For example, Chinese courts often will not recognise contracts or NDAs that would be enforceable in another jurisdiction. Government advice is available to help you consider this question if you are pursuing commercial opportunities in China.
- Will you give a prospective investor access to areas you would not give to other visitors?
- Do you control physical access to any sensitive assets or systems within your sites to only those individuals who need it?
- Have you taken steps to avoid the introduction of eavesdropping devices? This could include restricting access to sensitive areas. UK NACE, the UK's National Technical Authority for Technical Security, has further advice.
- Do you have physical security measures in place to detect if assets or systems have been accessed or compromised? Depending on resource and risk appetite, this could include using commercial Technical Counter Surveillance Measures.
- Do you use multiple layers of combined physical security measures to protect and compartmentalise your assets or systems?
- Are your systems appropriately designed to segregate sensitive networks and systems from those accessible to the wider organisation - including investors and overseas parties?
- Have you implemented technical measures to limit the data your investors can access to only what is necessary and appropriate?
- Are you applying similar levels of rigour to the information you divulge in any virtual demonstrations or tours as you would in person? NPSA have produced guidance on creating virtual tours.
- Personal electronic devices can be modified to act as eavesdroppers. Have you considered controlling the use of such devices in boardrooms and other areas where sensitive discussions take place?
- Acquisitions can result in organisational change. Have you completed a risk assessment of roles to ensure additional security arrangements are in place for people who require access to sensitive information or critical capabilities?
- Do individuals working with potential investors understand what can be shared and what must be protected?
- Do you conduct pre-employment screening on new starters and individuals moving into sensitive roles? NPSAs guidance on employment screening will help your organisation meet its legal obligations and set up a foundation for a safe and secure workplace.
- NPSA has a collection of guidance and tools designed to help your organisation reduce the risks posed by insiders.
- If your company conducts international travel, have you considered proportionate mitigation measures to protect your people and your critical assets when they travel abroad? This could include protecting any electronic devices taken overseas, removing non-essential data, and knowing what to share, trade, and protect.
- NPSA also has well-researched, robust and leading-edge tools to support your organisation to achieve an appropriate security culture, where the right security behaviours are adopted by the workforce.
Case study: use of combined mitigations
A small UK communication company had a number of contracts to produce sensitive technology for Government departments and private UK industry. The company was approached by a foreign investor.
Following a risk assessment, several mitigations were agreed which would protect the company's technology, reputation and chances of securing future Government contracts. This included:
- compartmentalising the company's most sensitive projects
- ensuring effective IT arrangements were in place to audit access to the sensitive information
- granting access only where necessary, and to individuals who had had the appropriate security checks
- identifying a Board-level owner of the risks associated with the transaction
These mitigations were agreed and fully implemented prior to the part-sale of the company.
Do you work or invest in international research collaboration?
The UK has a thriving research and innovation sector that attracts investment from across the world. However, hostile actors take advantage of research collaboration to gain unauthorised access to non-public information, sensitive research and personal information. Trusted Research is designed to help the UK's world-leading research and innovation sector get the most out of international collaboration while protecting its sensitive assets.
Ensuring your mitigations work
Commercial relationships can endure over a long period. The integrity of your mitigations will need to be maintained and monitored for the entire duration of the relationship. This may involve:
- Combining any mitigation with a structured approach to checking compliance and ensuring its ongoing integrity. NPSA has advice on network auditing. These legal considerations for employee IT monitoring may also help.
- Ensuring any new staff in critical roles either in your organisation or in the acquiring party are aware of the risks and agreed mitigations.
- Conducting a regular and ongoing review to ensure your mitigations stay current and reflect best practice.
Case study: limiting risk from an investor-appointed Board member
A UK semiconductor company was in negotiations for a foreign company to acquire a minority interest via the acquisition of shares. The foreign company stated that, as part of the acquisition, they wished to have the right to nominate a director to the Board.
Certain countries attempt to use international investment to gain influence over a company or sector.
To protect its interests and UK national security, the company:
- introduced measures (which will be regularly reviewed) to limit the access this Board member will have to the company's sensitive systems and data
- established a policy stipulating that the majority of the Board members must be UK nationals to limit external influence
- worked with NPSA and the NCSC to understand the risks and to establish appropriate mitigations
As part of your investment planning, you may also wish to consider sources of funding available from the UK public sector. The British Business Bank has information on a range of finance options through its Finance Hub.
What does the NSI Act mean for your business?

The UK Government has the power to call in for assessment a qualifying acquisition that could give rise to a national security risk. It will carry out a full assessment of the potential risks and, where necessary and proportionate, impose remedies to address identified risks. The UK Government can do so up to six months after becoming aware of the acquisition and within five years of the acquisition taking place.
If your organisation is within 17 defined areas of the economy, certain acquisitions set out in the notable acquisition regulations must be notified to the Government by the acquirer and receive approval from the UK Government before completing. If they complete without receiving approval, the acquisition will be void. BEIS has published guidance on types of acquisitions that can be classed as a notifiable acquisition at GOV.UK. Where a notifiable qualifying acquisition is not notified to the Government, the five-year time limit does not apply. Guidance on completing and registering a notification form is available.
Where a qualifying acquisition does not need to be notified, but still falls within scope of the legislation and may have a national security element, a seller, acquirer or the entity is encouraged to submit a voluntary notification. A Section 3 Statement is available to help assess the types of acquisitions that may raise national security concerns.
Further guidance on whether you need to tell the Government about an acquisition that could harm the UK's national security is available at GOV.UK.
Your obligations
The UK Government has powers to require that businesses and investors provide information in relation to its functions under the Act. This will help inform the national security assessment. You must comply with any requirement for information from the UK Government and with any remedies the Government may impose.
A number of sanctions civil and criminal will apply in the event of non-compliance. Civil and criminal sanctions are applicable, for example, where the acquirer has progressed a "notifiable acquisition" to completion without approval from the UK Government.
If you have identified any potential national security risks, engaging with the Investment Security Unit (ISU) early can provide clarity and avoid time-consuming barriers later in the process.
The Governments' obligations
The legislation provides a clear statutory process, which includes:
- publication of a Section 3 Statement providing guidance on the types of acquisition which the Secretary of State considers are more likely to give rise to national security risks this will be reviewed regularly
- time limits for the Secretary of State to assess cases and make decisions
This means that interactions with the UK Government will be simple and quick. A new NSI notification service has been established for qualifying acquisitions to be submitted through, and most acquisitions will receive clearance within 30 working days (and often quicker). Forms can be submitted to the notification service through this GOV.UK page.
Further details on the NSI Act are available at GOV.UK.
1. UK Tech Ecosystem update, Tech Nation, December 2020
2. British Business Bank, Small Business Equity Tracker 2021
All case studies are hypothetical examples